Are user credentials submitted during phishing simulations stored in BullPhish ID?
No. BullPhish ID focuses on simulation and training, not credential collection. When a user submits their credentials on a landing page during a phishing simulation, those credentials are not stored in the BullPhish ID system. For security and privacy reasons, the system only records that a credential submission occurred.
Only a limited set of non-sensitive evidence is recorded to confirm that the action took place.
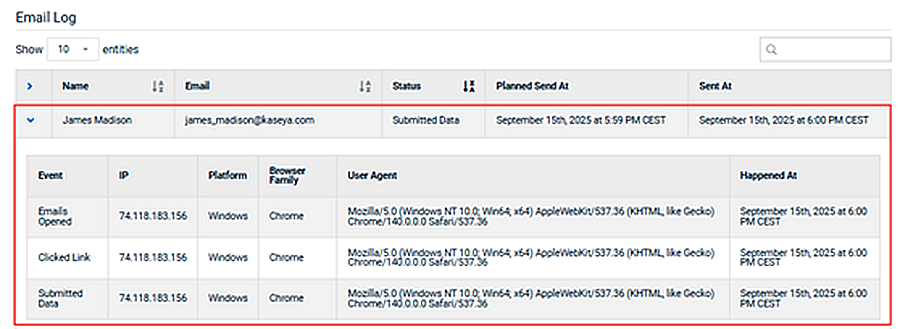
You can view the recorded data for a target who interacted with a phishing campaign in the Email Log on the campaign’s Details page. Expand the row for the desired target to see the captured data.
The Email Log includes the following information:
- Event: Identifies the action taken by the target. For example, opening the email, or submitting data, such as login credentials.
- IP: The IP address of the target's device.
- Platform: The operating system of the target's device.
- Browser Family: The browser used on the target's device.
- User Agent: Identifies the browser version and compatibility details for the target's device. Legacy-compatible versions are often included to ensure access to older sites.
- Happened At: The timestamp (in UTC) when event occurred.
This example shows three actions taken by the target, resulting in an event being created for each action.
In this example, the target took no action on the phishing email, so their event table is empty.
| Revision | Date |
|---|---|
| Initial release | 10/27/25 |